3250 Lyss
Schweiz - Switzerland
Secure, Digital Communication with Selectron Cybersecurity Products
The security by design concept comes into play in the development of cybersecurity products. In this context, security is primarily integrated into the development process.
Contact


Security by Design
Security influences every step from the definition of security requirements through to the development and certification of products, and maintenance. The dynamic environment, the constantly changing threat situation and newly discovered system weaknesses are challenges that must be mastered.
Accordingly, Selectron has introduced a security framework based on IEC 62443. This puts Selectron in a position to develop products according to standardized security levels in order to guarantee security over the entire lifecycle.
Defense in depth approach
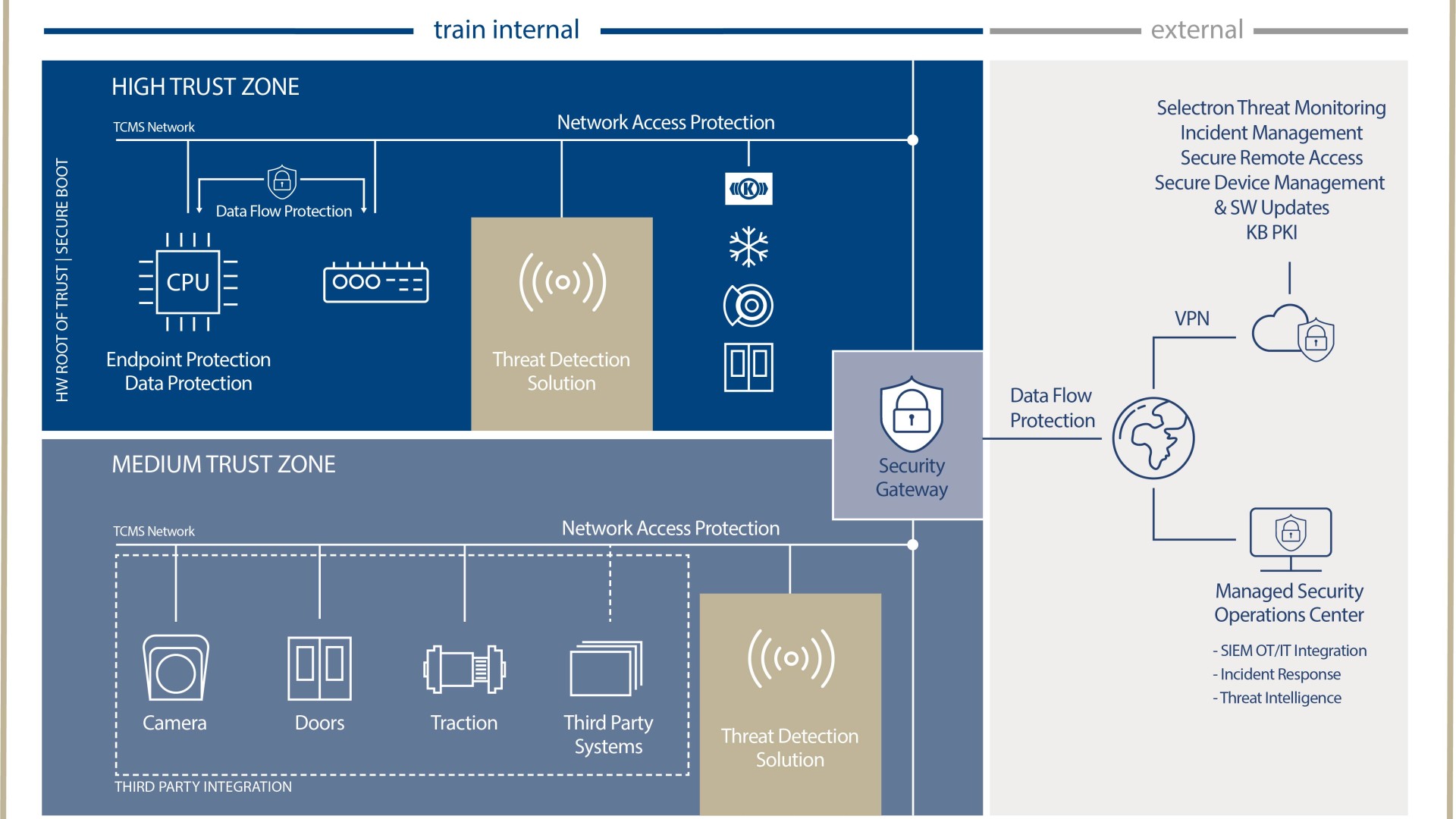
Security only functions within the overall system and therefore influences different products. The security role of a product is therefore defined taking into account the proven Selectron system. Based on the defense in depth approach, security is consistently implemented in the Selectron product roadmap:
- Protect: There are classic “security products” such as the Security Gateway (SGW) for network segmentation, “secure products” as secure variants of the classic TCMS components (e.g. Secure CPU) as well as the “security infrastructure”, which can be used for secure communication (PKI) among other things.
- Detect: The Threat Detection Solution (TDS) provides a cost-optimized solution for detecting anomalies in network traffic, especially for existing fleets. As a standalone measure, it can be used to cover important legislative requirements. In combination with other security measures and/or products, the information provided by the TDS from Selectron can make an essential contribution to trouble-free operation of a vehicle fleet. The solution has a modular structure and is therefore optimized for different application areas.
- Respond: Security updates are reliably provided thanks to the adapted processes. The targeted buildup of security expertise also enables us to offer services that complement our security portfolio, from risk assessments to incident management.
Considering this in the context of the overall system leads to the situation that important aspects such as usability need to be considered on a continuous basis despite all security requirements. Consequently, such aspects must be incorporated into the system architecture and thus into the designs of the individual products.